RhinOS™ 25 — Secure Enterprise
NAS Operating System
Proven. Hardened. Evolving.
RhinOS powers Ciphertex SecureNAS® systems in mission-critical environments, delivering military-grade security, ZFS data integrity, and modern container-based extensibility — all in a simple, hardened, appliance-ready OS.
Engineered for defense, government, healthcare, forensics, energy, and enterprise deployments that demand confidentiality, integrity, and resilience at the edge and in secure data centers.


What’s New in RhinOS™ 25
A major security and capability upgrade
New Capability
- Container Support Run approved OCI containers in a secure, isolated environment.
- Docker Local container development & deployment through Docker with embedded Portainer
- Kubernetes Large- and small-scale container orchestration through Kubernetes.
- Selectable TLS versions TLS version selection for compliance and zero-trust environments. Support environments needing older TLS 1, and TLS 1.1 through more secure TLS 1.2 and TLS 1.3.
- Enhanced firewall & access controls Strengthened network protection and service hardening with whitelisting and blacklisting by IP and service.
- Modernized Web UI Faster administration experience and improved system visibility.
- Up-to-date Security Continual updating to protect against the latest security threats and maintain optimal operation.
Customer Benefits:
Containers, Kubernetes & Enhanced Security
Modern workloads demand more than storage. RhinOS 25 transforms SecureNAS® into a secure application platform — enabling on-device analytics, automation, cyber defense tools, and modern DevOps workflows without sacrificing the hardened appliance security Ciphertex is known for.

Why Containers Matter for Customers
Containers provide a lightweight, controlled method to deploy modern tools directly on the SecureNAS® — without modifying the OS or risking system integrity.
Key Benefits
- Deploy tools securely without exposing the system to untrusted packages or full OS installs.
- Run isolated workloads (forensics tools, analytics modules, AI inference engines*, cyber defense agents).
- Zero impact to core NAS stability — containers run in sandboxed zones.
- Faster deployment cycles for new capabilities, patches, and mission-specific apps.
- Vendor-approved execution ensures only authorized containers can run.
- Future-proof architecture aligned with modern DevOps, automation, and edge-compute frameworks.
*Even legacy non-GPU units can run CPU-based AI inference, cyber analytics, and automation containers.
Robust Storage Capabilities
-
ZFS Architecture: Ensure data integrity with RAID-Z redundancy levels and proactive corruption detection.
- STRIPED => similar to RAID-0
- MIRROR => similar to RAID-1
- RAID-Z => similar to RAID-5
- RAID-Z2 => similar to RAID-6
- RAID-Z3 => similar to RAID-7
- Striped RAID-Z => ZFS-Striped of RAID-Z/2/3
-
Deduplication & Compression: Optimize storage space and performance with block-based data deduplication and inline compression (LZ4, LZJB, ZLE, GZIP 1.9).

Scale up or scale out with ZFS.
ZFS architecture works similarly to traditional hardware RAID, except it uses smaller RAIDs in partitions called “Vdevs”, or virtual devices. ZFS detects silent data corruption better than traditional RAID and it writes data to a log before writing to storage blocks — if a drive fails or the system shuts down unexpectedly, the cached log will store the writes-in- process until ZFS determines it’s safe to resume.
How RAID-Z Differs from Traditional RAID Systems
ZFS RAID-Z is a file system and logical volume manager that introduces advanced features and functionalities that set it apart from traditional systems. One of the standout features of ZFS RAID-Z is its end-to-end data integrity through its checksumming feature. The system computes a checksum every time data is written to or read from a disk and compares it to the original to ensure data integrity.
Unlike traditional RAID, which relies on hardware controllers for data redundancy and performance, ZFS RAID-Z handles these functions at the software level. It eliminates the need for expensive hardware controllers and allows for more flexibility and customization. Additionally, ZFS RAID-Z offers features such as data compression, deduplication, and snapshots, making it a robust and versatile storage solution.

Striping is the process of distributing blocks of data across hard drives. Input data is split up into pieces known as striped units. If you refer to this diagram, striped units Block 0 through Block 8 would be considered a stripe.
A single hard drive handles read and write operations one at a time. In contrast, a RAID 0 system enables parallel processing, allowing the system to perform read and write operations across multiple drives simultaneously. For example, the owner of a striped system can access Block 0, Block 1, and Block 2 at the same time, significantly improving performance.
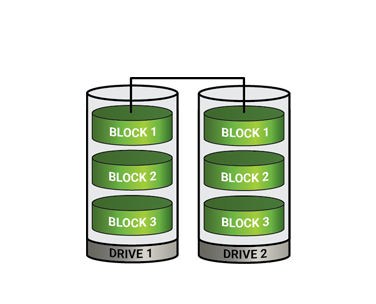
Mirroring writes all data simultaneously to two drives, creating a 1-for-1 copy that offers the highest level of redundancy. This setup also delivers excellent read performance, as the system can access both drives in parallel. Write performance remains steady because both drives write the same data at the same time. However, RAID-1 comes with a higher cost since it requires double the storage capacity to mirror data. Traditional RAID-1 supports only two drives, which limits its scalability for larger storage needs.
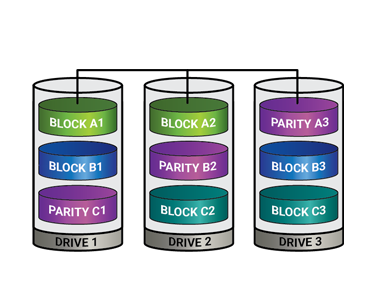
RAIDZ provides redundancy by using parity, allowing data recovery without the need for full duplication on a second drive. It mathematically creates a new block of data across multiple disks, so if one drive fails, the RAID controller can reconstruct the missing data from the remaining drives. RAIDZ supports single parity, enabling the system to continue functioning even if a drive fails, with parity distributed across the disks to balance access and improve performance. While RAIDZ offers high storage capacity and reliability, performance is slightly reduced due to the calculations required for reading and writing data.
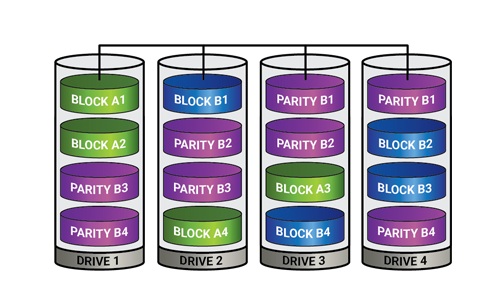
RAID-Z protects against a single drive failure and can actively rebuild the data. RAID-Z2 goes further by using two separate sets of parity calculations, allowing it to recover from two simultaneous drive failures—what’s known as N+2 redundancy. To function properly, RAID-Z2 requires at least four drives: two for data and two for parity. It performs best when used with a larger number of disks, though only to a certain point. As disk count increases, so does efficiency—but also the risk of multiple failures and the complexity of rebuilding. RAID-Z2 strikes a strong balance between capacity, redundancy, and performance, making it the preferred choice for high-capacity storage environments.
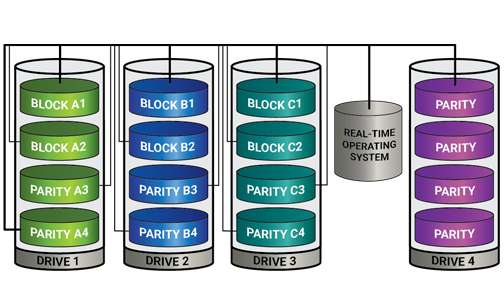
RAID-Z3 is the most advanced level of RAID-Z, offering triple-disk redundancy. It can withstand the failure of up to three disks without losing any data. RAID-Z3 is ideal for environments where data integrity is critical and cannot afford any data loss.
Benefits of Kubernetes Integration
Kubernetes brings orchestration and scale to secure environments — even when running as a Worker Node.
- Distributed workloads across multiple SecureNAS units (threat analysis, scanning, metadata tagging, microservices).
- Enterprise-grade automation for container updates, failover, and scaling.
- Hybrid-edge deployments for defense, field forensics, and remote industrial sites.
- Secure participation in larger enterprise clusters without exposing the NAS OS to the public internet.
- Consistent workloads from dev → test → production, even in air-gapped environments.
RhinOS™ 25 brings “data-plus-compute” to the edge — securely.
Enhanced Security: Real Operational Value
RhinOS 25’s strengthened zero-trust framework directly
improves mission assurance.
Advantages to the customer
- Selective TLS (1.0 → 1.3) ensures compatibility with legacy agencies while enabling modern, secure protocols.
- IP Whitelisting/Blacklisting prevents unauthorized hosts from communicating with the system.
- Hardened services reduce the attack surface for bad actors.
- RBAC + AD/LDAP ensure only the right personnel access sensitive datasets.
- Encrypted communication & storage protect data in motion and at rest — even in contested environments.
- Container isolation prevents application-level vulnerabilities from impacting core system functions.

Security & Compliance
Confidential computing at the core
- FIPS 140-2 hardware encryption key integration
- TLS 1.2+ encryption (selectable protocol versions)
- Role-Based Access Control (RBAC)
- Active Directory / LDAP integration
- Secure USB port lockdown
- Built-in antivirus & firewall protection
- Multi-layer encryption — data at rest & in transit
Zero-trust principles. Military-validated hardware. Rugged security everywhere.
Rapid Return on Investment
ZFS Data Integrity & RAID Protection
RhinOS delivers enterprise-grade data protection using the OpenZFS file system, ensuring fault tolerance, integrity, and high availability in mission-critical environments.
RAID Mode | Equivalent To | Protection | Best For |
Mirror | RAID-1 | Survives 1-disk failure | Highest redundancy, high-performance reads |
RAID-Z1 | RAID-5 | Survives 1-disk failure | General secure NAS workloads |
RAID-Z2 | RAID-6 | Survives 2-disk failures | Mission-critical, forensic, healthcare, gov |
RAID-Z3 | RAID-7 | Survives 3-disk failures | High-availability + high-capacity clusters |
Striped Mirror | RAID-10 | Survives multiple disk failures | More capacity with higher speed |
Striped Z1 | RAID-50 | Survives multiple disk failures | More capacity with higher speed |
Striped Z2 | RAID-60 | Survives multiple disk failures | More capacity with higher speed |
Striped Z3 | RAID-70 | Survives multiple disk failures | More capacity with higher speed |
Key Advantages
- End-to-end checksumming with automated repair
- Self-healing data paths
- Inline compression & deduplication
- Petabyte-scale expansion via VDEVs & pooling
- Up to triple-parity protection
Secure Container & Kubernetes Execution
Run secure containerized services with integrated Kubernetes support — designed for controlled enterprise and mission-critical environments.
- OCI container support
- Local container development, testing, and deployment through Docker and a special local version of Portainer
- Kubernetes-enabled runtime for Cluster participation
- Kubernetes Worker-Node capability for secure, scaled distributed container workloads
- Isolated execution environment for high-security deployments
- Deploy forensic tools, cyber defense agents, analytics modules & secure workloads
- Preserves appliance-grade security posture
Enterprise File & Block Services
Flexible multi-protocol access to meet any IT workflow
- SMB/CIFS with AD support
- NFSv4
- iSCSI block storage
- Rsync client/server
- WebDAV & SFTP/FTP
- USB share support
Mix secure file-sharing, SAN, backup, and remote workflows seamlessly.
Virtualization & Edge Compute Support
Run controlled virtual machines for secure tasks and isolated workloads
- VirtualBox-enabled VM support
- Windows, Linux, BSD and proprietary guest OS options
- RDP access
- Simple import/export across virtualization platforms
Forensics, cyber tools, and system appliances — without external infrastructure.
Backup, Replication & Recovery
Built-in data durability and ransomware resilience
- Duplicati-based encrypted backup
- Multi-site replication
- Cloud backup targets (Azure, AWS S3, Google Cloud, etc.)
- Schedule or manual sync jobs
- USB one-touch backup
- Volume/LUN snapshots & instant restore
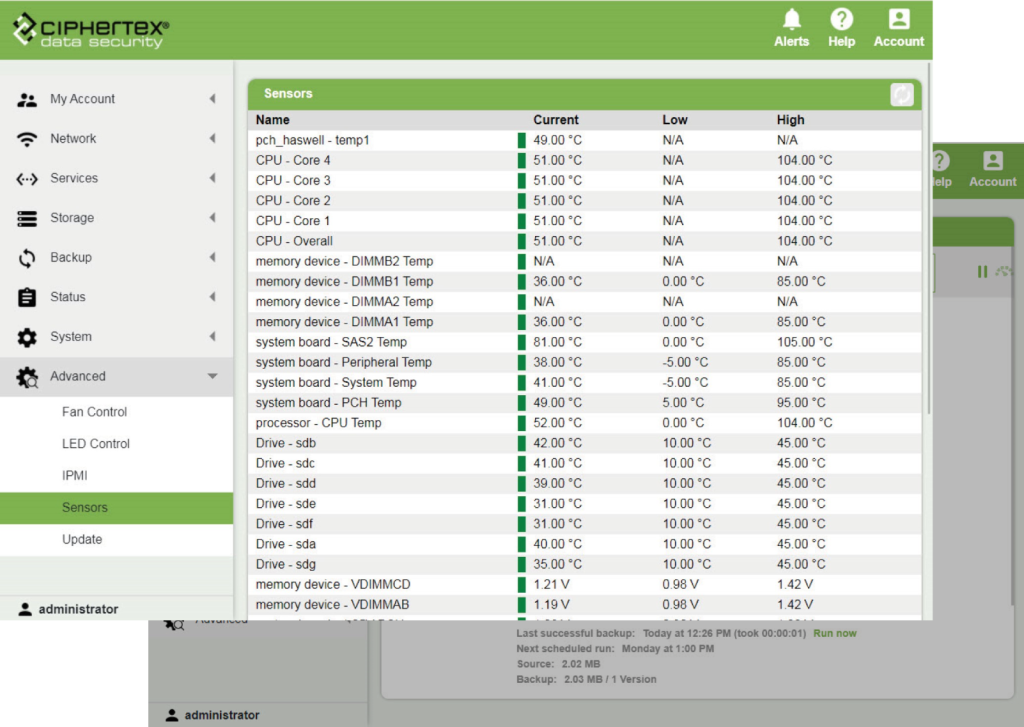
Management & Monitoring
Simple control for complex secure environments
- Web-based management console
- Real-time health monitoring & alerting
- SNMP integration
- Remote config backup/restore & system updates
- Front-panel LCD/LED status
- Remote power and shutdown

For Secure & Regulated Use Cases
Validated across demanding environments:
- U.S. military & defense missions
- Federal & state government
- Law enforcement & digital forensics
- Healthcare & HIPAA environments
- Energy, oil & gas, and remote industrial sites
- Cybersecurity labs & critical infrastructure
Trusted where failure is not an option.
Customer Testimonials at bottom and raid calculator link will remain same as before.