In a substitution cipher, single letters, pairs of letters, or groups of three letters (or any combination of these) are changed, but the order of the letters stays the same. Simple substitution ciphers use single letters, whereas polygraphic ciphers use larger groups of letters.
In plain terms, letters are substituted for other letters. In the past, corresponding characters could be written out in the past so a message could be decrypted. Substitution ciphers are also used in modern cryptography. Bit-oriented block ciphers are more abstract and employ a large binary system.
The History
Cipher systems were used during World War I for tactical communications. The concept had been around for centuries. But during this time, it advanced from an unsophisticated cipher disk used by the U.S. Signal Corps to more complicated systems employed for high-level communications. A rotor cipher machine was built in 1917 and the idea was developed through the 1920s. It would eventually become a key communication tool during World War II by Nazi Germany.
What Is the Enigma Machine?
The Enigma Machine, invented by German engineer Arthur Scherbius, used an electromechanical rotor mechanism to scramble all 26 letters of the alphabet. Its rotor settings and wiring arrangements enabled it to replace characters in a message with each keystroke. These settings would be arranged between the sender and receiver. The German military would even double-encrypt messages by replacing messages with code words and then enciphering them.
Who Cracked the Enigma Code?
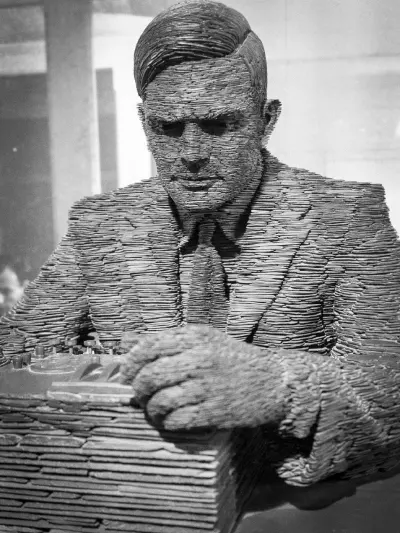
Alan Turing, a computer pioneer and cryptanalyst known for his work in artificial intelligence, helped to break the Enigma code in Britain. He developed a device in 1939 that could decipher German encryptions. Turing’s method was used extensively from 1941 to 1943 to break the even more complicated Naval Enigma system, a breakthrough which helped avoid German U-boats during a major battle. This was invaluable since decrypted messages often contained information on foreign military, espionage, and sabotage activities.
Why Our Brand Is Ciphertex®
Data security is more important than ever because nearly all data is digital, including business documents, emails, and personal information. Security threats are constantly evolving. Therefore, advanced encryption is essential. Our brand is defined by the concept of ciphertext because we are a leader in data security solutions. Our President and Chief Executive Officer, Jerry Kaner, has an extensive background in cryptography and computer science. He led one of the first teams to develop advanced storage technology and high-speed communication systems for U.S. military satellites. He is also known for developing advanced data recovery, computer forensics, and high-performing storage systems.
Today, Ciphertex® is a leader in data security software and integrated hardware-based AES 256-bit encryption and RAID storage technologies. We also offer rugged, portable Network-Attached Storage (NAS) and Direct-Attached Storage (DAS) systems. Onsite hardware support and software development services are available as well. Call 877-977-8878 or 818-773-8989 or email info@ciphertex.com to learn more.
